Category: Google Chrome
Google Chrome, Firefox, Safari And Possibly Opera Affected By Memory Leak

According to TNW, Internet Explorer is the only modern web browser (Opera was not tested due to temporary issue with the test page) that is not affected by the recently found memory leak.
One of the developers has created a test site with the Google’s App Engine to demonstrate the issue.
Once the site is back online, users can reproduce the bug by following these steps:
Continue Reading
Test Linux In Your Web Browser
Yes, you can now run Linux in your Linux while you Linux.
Fabrice Bellard, the author of QEMU, an open source machine emulator and virtualizer, has created a PC emulator in JavaScript.
How is this news? Thanks to various advancements in the web browsers, curious Google Chrome 11 and Firefox 4 users can now play with the actual Linux terminal in just under few minutes!
All you have to do is open the following page. That’s it.
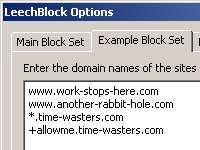
Google Chrome, Firefox: Block Specific Sites With LeechBlock And StayFocusd
If you are looking for a great way to boost your productivity by blocking certain sites and the specific time of the day, then Google Chrome or Firefox are the browsers to user.
LeechBlock
WebGL: iOS RAGE

Earlier this year, RAGE, the upcoming 3rd person shooter from the id Software (set for September release) has received an iOS version of the game.
Now, Brandon Jones, the US based software developer took one step further and rendered it with WebGL. That’s right, RAGE running in your web browser!
Continue Reading
Weekly Browsers Recap + Bonus Links, May 16th

FavBrowser.com
- Firefox about:config Preferences Explained
- Firefox 4 Market Share Increases 30% After Upgrade Offer
- Chrome Hack Denied By Google Engineers
- Google’s Chrome Sandbox Hacked
- Google Chrome 12.0.742.30 Beta Brings Fancy Features
- Google Chrome: 160 Million Active Users And Growing
- Google’s Dear Sophie: You Are Doing It Wrong
- Chrome Web Store, Now Available Worldwide
- How to Unlock All Google Chrome Angry Birds Levels
- Remote Debugging with Safari Web Inspector / Chrome Developer Tools
- Opera To Fix Default Installation Behavior
- Opera Software Q1 2011 Financial Results
- Opera: Enable New Google Image Search Interface
- Web Browsers: iPhone 4 vs. Samsung Galaxy S II vs. HTC Thunderbolt vs. Samsung Focus
- Wikitude: 3D Augmented Reality Browser
- WebGL: Play Angry Birds For Free
- WebGL Awesomeness: 3 Dreams Of Black
- LastPass May Have Been Hacked
- Download Adobe Flash Player 10.3 Final
Who Here Is Getting A Chromebook?
I am rather curious about this matter. Although Google Chrome OS is an operating system, it is an operating system that consists of only a web browser. It boots you into an enhanced version of Google Chrome and you do what you need to do from there. It has never been done before to my knowledge, and since major browser vendor Google is pushing this project with all that it’s got, Google Chrome OS may very well be here to stay. Who knows, perhaps Opera, Mozilla, or even Microsoft will follow?
Continue Reading
Chrome Hack Denied By Google Engineers
 As reported previously by FavBrowser, Google Chrome’s sandbox has allegedly been hacked. Nevertheless, several security engineers over at Google have now denied this, countering claims that a security company discovered a vulnerability in Chrome that could let attackers hijack Windows PCs running the browser.
As reported previously by FavBrowser, Google Chrome’s sandbox has allegedly been hacked. Nevertheless, several security engineers over at Google have now denied this, countering claims that a security company discovered a vulnerability in Chrome that could let attackers hijack Windows PCs running the browser.
The bug that security company Vupen exploited to hack Chrome was in Adobe’s Flash which comes bundled with Chrome, not in Chrome itself, said the engineers. A Google spokesman said that investigation was still ongoing, but the engineers decided to make themselves heard.
Continue Reading
How to Unlock All Google Chrome Angry Birds Levels
 Works with all web browsers.
Works with all web browsers.
Not interested in going through all Angry Birds levels, one by one? Worry no more; there is a solution for that.
To unlock all levels, type the following code in the address bar
javascript: var i = 0; while (i<=69) { localStorage.setItem(‘level_star_’+i,’3′); i++; } window.location.reload();
Revert
javascript: var i = 1; while (i<=69) { localStorage.setItem(‘level_star_’+i,’-1′); i++; } window.location.reload();
Enjoy.
Via: Technorati
Download Adobe Flash Player 10.3 Final
 The final version of Adobe Flash Player 10.3 has been just released for both desktop computers and mobile devices.
The final version of Adobe Flash Player 10.3 has been just released for both desktop computers and mobile devices.
What’s New?
Media measurement
Acoustic echo cancellation
Simplified local storage management
Auto-update notification for Mac OS
Local settings manager
For a detailed list of changes, see the following page.
WebGL Awesomeness: 3 Dreams Of Black
If you are a fan of WebGL technology, then this gem is definitely worth checking out.
“3 Dreams of Black” by Rome is an interactive video made using WebGL which just shows you the possibilities amazing future of the web.
WebGL support is a must for your web browser, so in case you don’t use Google Chrome or Firefox, grab it now and open the following link.
Enjoy.