Category: Security
Google Chrome Rewards Increased By $1,000
 Or more…
Or more…
Even though Google has already paid more than $1 million dollars for bug reports, the search giant has recently announced that they will be increasing the budget for its Chromium Vulnerability Rewards Program. According to the official blog post, bug hunters will now receive a bonus of $1,000 or more for every security flaw discovered.
Continue Reading
Google Chrome 21 Final Improves Adobe’s Flash Plugin Security And Performance
 Windows and Linux only.
Windows and Linux only.
Thanks to a sharp focus, Google Chrome engineers are able to work just on a few, rather than dozen features at the same time, delivering stable rather than clunky web experience.
Now, according to the recent blog post, the latest final build of the Google Chrome 21 web browser improves something what really matters: security.
Continue Reading
Mozilla Blocks Ubisoft’s Uplay Plugin
 This is why we can’t have nice things.
This is why we can’t have nice things.
Uplay, a browser plugin that appears on your PC once you install various Ubisoft games, has been discovered to have a serious security vulnerability, which allows malicious websites to take over your computer.
Now, according Mozilla’s blocked plug-Ins list, the open source organization took appropriate steps and has since blocked the mentioned crapware.
On a related note, Ubisoft has just updated its Uplay client to version 2.0.4, supposedly fixing the mentioned vulnerability.
Google To Pay $22.5 Million For Users Tracking
 As reported earlier, Google has bypassed the cookie settings in both Apple’s Safari and Microsoft’s Internet Explorer web browsers. Thankfully, it wasn’t left unnoticed by the Federal Trade Commission.
As reported earlier, Google has bypassed the cookie settings in both Apple’s Safari and Microsoft’s Internet Explorer web browsers. Thankfully, it wasn’t left unnoticed by the Federal Trade Commission.
Now, according to the WSJ, Google is close to a settlement, which would require them to pay a total of $22.5 million to the FTC.
Continue Reading
Watch Windows Phone 8 Summit (Full Video)
With Internet Explorer 10 and more.
If you are curious to see the upcoming IE10 browser in action, check the full Windows Phone 8 Summit video above. Not interested in everything? No worries, browsers start at: 15:00 and 39:00!
Alternatively, check our recent post about the very same presentation.
Mozilla, Microsoft Not Happy With CISPA
As “shocking” as it might sound, it looks like everyone’s hated CISPA is not supported by Microsoft and Mozilla as well.
Citing privacy concerns, both corporations have issued the following statements:
Continue Reading
Google Goes Mental: Increases Chrome Rewards To $20,000
If previous cash rewards were not enough to encourage you to start sniffing the code, then we have some good news.
Continue Reading
Firefox Blocks Old Java Plugins
 Good news for Firefox users, thanks to the never ending Java vulnerability spree, Mozilla has decided to protect its users and from now on will block Java plugins with a Version 6 Update 30 and below as well as Version 7 Update 2 and below.
Good news for Firefox users, thanks to the never ending Java vulnerability spree, Mozilla has decided to protect its users and from now on will block Java plugins with a Version 6 Update 30 and below as well as Version 7 Update 2 and below.
According to the official blog post, the February update for the Java Development Kit fixes a critical vulnerability, which prevents hackers from running exploit on user computer.
However, for those who want even more security, here is a simple tip: uninstall Java.
IE9 Hacked, Chrome Pwned (Again)
Security flaws everywhere.
After Google Chrome has been hacked twice, Microsoft’s Internet Explorer 9 was the second browser to fail the security challenge.
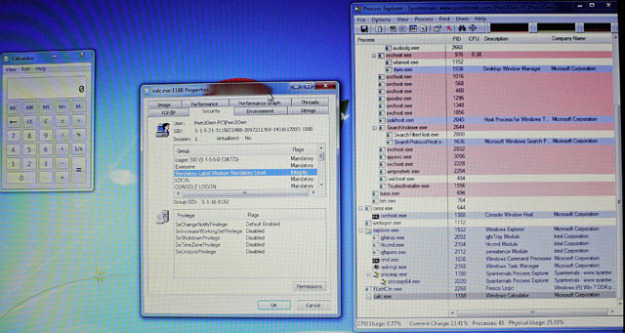
By exploiting two unknown vulnerabilities, Vupen Security was able to remotely open a calculator running on a Windows 7 SP1 machine. While no additional details were revealed, both IE and Google Chrome exploits were a combination of at least a couple of previously unknown flaws.
Continue Reading
Google Chrome Pwn2Own Vulnerability Patched

From left to right Jim Hebert, Cris Necker, Justin Schuh
Just 24 hours after reporting the critical vulnerability in Google’s Chrome web browser, the search giant has already released a patch to address the issue.
Identified as a bug CVE-2011-3046, discovered vulnerability is described as “UXSS and bad history navigation”, with no additional details revealed.
Continue Reading



