Category: Google Chrome
Sony to Offer Chrome Web Browser on Their PCs
 Google and Sony have signed a deal which states that Chrome web browser will be pre-installed on Sony PCs. Unfortunately companies have not revealed any financial or specific model details.
Google and Sony have signed a deal which states that Chrome web browser will be pre-installed on Sony PCs. Unfortunately companies have not revealed any financial or specific model details.
According to IDC research, consumer electronics giant Sony is not in the top 5 PC vendors by worldwide shipping as per Q2 2009.
Calling this partnership experimental, Google is looking forward to sign similar deals with other PC makers as well.
Update: Financial Times reports that Chrome will be per-installed on Sony’s Vaio computer series.
Weekly Browsers Recap, August 31st

- Microsoft: No IE 8 tab-hang fix in the works
- Internet Explorer 8 Moves into Businesses
- Firefox 4.0 goes Chrome, will arrive with new UI in Q4 2010
- Three Firefox Add-Ons are Faulty!
- Google Chrome Updates with Security Fixes
- Opera Mini Is Most Downloaded Mobile App
- The long road to HTML 5
Thanks to Trygve Lie for links.
Weekly Browsers Recap, August 24th

- Firefox 3 about to get a major update
- Please tell me Firefox won’t ever look like this on first run. (Picture)
- Seeking web security, exploit operators prefer Firefox, Opera comes second
- Google Chrome 4 reveals the beginnings of cloud synchronization
- Xmarks extension alpha for Chrome arrives
- HTML 5 and timed media
Thanks to Chrome, Nox and Opera for links.
Google Chrome 64 bit (x64)
Good news for Linux users. After quite a few changes, 64 bit version of Google Chrome (Chromium) 4 has been released for Ubuntu operating system.
You may download the latest build here and use the following instructions to compile it.
[digg-reddit-me]
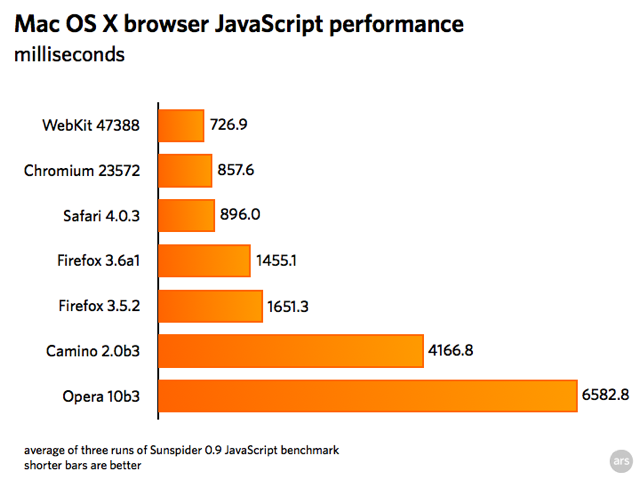
OS X: WebKit Outeperforms Chromium in JavaScript Benchmark
Ars Technica reports that the latest build of WebKit has outperformed Chromium by more than 15% in SunSpider benchmark.
They have also tested Safari 4.0.3, Firefox 3.6 Alpha 1, Firefox 3.5.2, Camino 2.0 Beta 3 and Opera 10 Beta 3 web browsers.
NSS Security Test: More Details Emerge
 Here are some more details from Ars Tecnica, which should clarify Microsoft and NSS Labs “sponsorship” deal.
Here are some more details from Ars Tecnica, which should clarify Microsoft and NSS Labs “sponsorship” deal.
In terms of sponsorship of the reports, “this stuff is expensive to do right, and we need to monetize it somehow,” Moy told Ars. “We invited Google, Mozilla, Apple, Opera to participate, but they didn’t even bother to respond, except for Opera, which stated they “don’t really focus on malware.”
Also, readers have noticed that Firefox 3.5 was not included in those tests, here is a reason (as from .pdf).
We would have liked to have been able to test Firefox 3.5 which was released on June 30, 2009, and attempted to test it alongside the other browsers. However, serious instability where the browser repeatedly crashed (a widely reported issue) along with poor results prevented its inclusion for the sake of fairness.
For NSS Security Test results, see the following page.
[digg-reddit-me]
Weekly Browsers Recap, August 17th

- Microsoft Extends Internet Explorer 6 Support To 2014
- Invisible Hand Plug-In Points Out Better Deals
- Futz.me Turns Your Browser’s Address Bar into a Command Line
- Opera, Chrome Not Officially Supported by Office Web Apps
- Safari plug-ins that improve your browsing
- RIM says BlackBerry Browser Will Match Mobile Safari Next Year
- Dell Likes Ubuntu, But Has Eyes On Chrome
Google Chrome OS Screenshots
Mashable has posted possible screenshots of the upcoming Google Chrome OS.
Chrome 4 in the Works

Picture Source: cNET
Although Chrome 3.0 is still in Beta, Google engineers have already started to work on Chrome 4.0 web browsers and revealed first pre-alpha builds.
As Anthony LaForge explained: We’ve officially bumped Chromium to 4.0.x to reflect our code freeze point for 3.0. There is still a bit of work that needs to be done for 3.0 in terms of stability and fixes, and to that end we will be pulling changes into the 195 branch (what will become the stable release).
Chrome 4.0 does not bring any significant changes yet, when compared to the latest 3.0 Beta snapshot.
You can download latest builds from the following page.
Via FM_Peacekeeper (Twitter)
[digg-reddit-me]
Opera Chief Warns on Equal Access to Windows Services
 The Register writes:
The Register writes:
Microsoft might be closer to a compromise with browser rival regarding Internet Explorer on Windows, but access to key online services for PCs could be the next hurdle.
Opera Software chief executive told The Reg he welcomed Microsoft’s offer last month to give European PC users a choice of browsers on Windows, but he warned of “problems” if rival browsers don’t get equal access to crucial sites that help keep users’ PCs secure and updated.
[Read]